Patent application title: ANTI-TAMPER PROCESS TOOLSET
Inventors:
Joseph Di Beneditto (Great Falls, VA, US)
Assignees:
Raytheon Company
IPC8 Class: AG06F1730FI
USPC Class:
707741
Class name: Database and file access preparing data for information retrieval generating an index
Publication date: 2013-02-07
Patent application number: 20130036123
Abstract:
A tool set is provided that uses a series of modules (e.g. spreadsheet
workbooks) for assessing risks/threats to and attacks against a project
and developing countermeasures against such risks/threats/attacks. The
project may cover a wide berth of functionality from alarm systems,
computer security, building projects, etc. The roll up feature of the
spreadsheet may be employed to evaluate changing scenarios in a short
period of time. Ranked threats and countermeasures operable to defeat
such threats may be displayed in a tree diagram generated by one or more
of the modules.Claims:
1-8. (canceled)
9. A method of generating a tamper tree diagram comprising: assigning hierarchical indices to individual data elements for computer data records; combining hierarchical indices for each data element in a computer data record into a single mine and sortable composite record index; sorting composite record indices; extracting individual hierarchical indices from sorted composite record indices; determining a hierarchical attack tree stud=from extracted individual hierarchical indices; and replacing hierarchical indices with actual associated data elements.
10. A system evaluating possible countermeasures against elements of a project comprising: the project; programmable computer useable medium operable to cause said computer to process data records concerning risk, threat, vulnerability impact and security attack, said medium being further operable to cause said computer to apply an algorithm to said data records to rate time-factored risks and select appropriate countermeasures and technical implementations therefor against said time-factored risks, said medium being programmed to cause said computer to generate a tamper tree diagram by assigning hierarchical indices to individual data elements for computer data records; combining hierarchical indices for each data element in a computer data record into a single unique and sortable composite record index; sorting composite record indices; extracting individual hierarchical indices from sorted composite record indices; do hierarchical attack tree structure from extracted individual hierarchical indices; and replacing hierarchical indices with actual associated data elements.
11-24. (canceled)
Description:
BACKGROUND
[0001] Project development, whether involving building construction, government contracting, software development or the like, requires planning for contingencies which may arise affecting completion or implementation of the project. Some contingencies may involve deliberate attempts to cause failure such as security system tampering. In such an instance, the project should be able to defeat the tamper attempt, Planning for such contingencies of project tampering is usually done on an ad hoc non systematic basis. Until now, no robust anti-tamper planning measures have been available.
BRIEF DESCRIPTION OF THE DRAWINGS
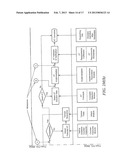
[0002] FIG. 1 illustrates a diagram showing the anatomy, i.e., both the functional layout of an anti-tamper process toolset and its process flow, of the anti-tamper process toolset.
[0003] FIGS. 2A-2M illustrate operational modules (e.g. Excel®--based workbooks) operable to carry out the anti-tamper process toolkit.
[0004] FIG. 3 illustrates an Attack/Tamper tree diagram.
[0005] FIG. 4 illustrates a typical database form in the anti-tamper process toolset.
[0006] FIG. 5 illustrates a threat/attack summary worksheet.
DETAILED DESCRIPTION
[0007] A system and method are provided for identifying and analyzing attacks against, risks/threats to and countermeasures against projects/project goals/assets including security related functions, government contracting projects, etc,.
[0008] FIG. 1 illustrates a diagram showing the anatomy, both the functional layout of an anti-tamper, process toolset and its process flow, of the anti-tamper process toolset for accomplishing the foregoing, For a given project, particularly involving security, a number of measures may be taken to defeat the very purpose of a particular project protocol, device, method, system, etc. The project protocol, device, method or system may relate to a defense system, security system or even a relatively simple alarm system for a home business or automobile. For instance, a monitored alarm system may include a wireless transmitter for notifying a monitoring station in the instance of an alarm event in case a telephone landline is not functioning (e.g., telephone wires have been cut during a burglary). The wireless transmitter serves as a countermeasure taken against the alarm system in an instance where tampering of the monitoring capability of the alarm system has occurred (e.g., telephone monitoring wires cut). For any given alarm system, there are a host of threats/attacks (threats and attacks are used herein interchangeably) that may occur which should be contemplated in advance of the system's design so that proper measures may be designed-in to properly defeat tampering, properly allocate funding for countermeasures against such tampering and properly assess and allocate tampering risks in the design of the alarm system.
[0009] The elements shown in FIG. 1 may be carried out using a series of workbooks, i.e. modules. In one aspect, the workbooks may be presented as a suite of highly automated and fully integrated workbooks. Workbooks represent a functionality found in spreadsheet programs such as Microsoft® EXCEL* or IBM® Lotus® 1-2-3®. Such workbooks may be implemented according to, for instance, a couple of thousand lines of Visual Basic® automation code using modules. Program initialization and upgrades may likewise occur in connection with using modules. Further, a hidden database module having anti-tamper protections may be used to provide near-immediate data updates for other modules.
[0010] Operational modules (e.g. Excel®--based workbooks) operable to carry out the anti-tamper process toolkit are described below and illustrated in FIGS. 2A-2M.
CPI Tool Workbook
[0011] This workbook is illustrated in FIG. 2A and guides the user through the CPI (Critical Program Information) evaluation process to determine which items within the subsystem can meet CPI criteria. If an item is determined to be Critical, it is automatically assigned an Asset ID number for tracking throughout the other modules of the AT Toolset.
WBS CPI Workbook
[0012] This workbook is illustrated in FIG. 2B and provides a means for cross-referencing CPI criteria versus contractor Work Breakdown Structure elements.
[0013] Asset ID and Valuation Workbook
[0014] This workbook is illustrated in FIG. 2C and allows for an automatic roll-up of the CPI (Assets), for input of additional description and value information about each Asset, and assignment of an Impact rating if the Asset were totally lost. In general, for all workbooks, the roll-up feature of a spreadsheet program may be employed in order to run several changing scenarios in short order.
Threat and Vulnerability Workbook
[0015] This workbook is illustrated in FIG. 2D and allows for an automatic roll-up of data gathered in previous workbooks, for definition of possible threats to the subsystem, and for input of susceptibility ratings of the threats against each Asset in each of the various environments that the subsystem will be subjected to throughout its life. The data is ultimately transformed into the susceptibilities of each Asset to the various threats in each environment. This form of the data allows for the worst case exploitation analysis against each Asset.
Attack Workbook
[0016] This workbook is illustrated in FIG. 2E and allows for an automatic roll-tip of data gathered in the previous workbooks, for definition of possible Attack scenarios against each Asset, for input of the likelihood of each Attack and assignment of impact rating of a successful Attack. It may utilize a unique algorithm to automatically generate an Attack Tree diagram for the Subsystem based upon the data input in this and previous workbooks.
Risk Workbook
[0017] This workbook is illustrated in FIG. 2F and utilizes the data gathered in the previous workbooks to perform an exploitation risk computation. A worst-case initial and a time-factored Risk rating is computed for each Asset. The CPI Evaluation Tool, Asset ID and Valuation, Threat and Vulnerability, and Amok workbooks must be filled in prior to using this workbook.
Countermeasures Workbook
[0018] This workbook is illustrated in FIG. 2G and takes the outputs from the previous workbooks and displays a Worst Case/Negligible Risk status of each Attack against each Asset. Countermeasure methods are defined, as required, and the user goes back to previous workbooks to adjust parameters based upon the Countermeasure application, and a new worst-cast Risk Analysis is performed based upon the results. initial and final Time-Factored Risk levels are recorded. The Initial Time-Factored Risk for each Attack scenario is recorded before any countermeasures are utilized. Final Time-Factored Risk for each Attack scenario is recorded after countermeasures, if required, are applied and analyzed. If countermeasures are not required, then the Final Time-Factored Risk for the Attack scenario is recorded at the same time that the Initial Time-Factored Risk is recorded. When Final Time-Factored Risk is recorded, that Attack scenario is automatically turned of and the next Worst-Case Attack on the Asset is assessed, The Attack, Asset ID and Valuation, Threat and Vulnerability, and Attack workbooks must be filled in prior to using this workbook.
Concepts Selection Workbook
[0019] This workbook is illustrated in FIG. 2H arid takes the outputs from the Countermeasures workbook and leads the user through the AT Concept selection process, Available AT techniques are entered, Concepts developed based upon layered AT Techniques, as necessary, and an AT Concept solution set is selected for each Countermeasure requirement established in the Countermeasures workbook.
Implementation Parameters Workbook
[0020] This workbook is illustrated in FIG. 2I and provides for an automatic roll-up of countermeasure requirements analysis from previous workbooks, and for the input of specific contract requirements for each Countermeasure and definition of the V&V (Verification and Validation) methods that will be used to confirm successful treatment of Risk.
Health Status Workbook
[0021] This workbook is illustrated is FIG. 2J and documents Sub-system and overall system AT progress status.
[0022] Toolset Initialization Workbook
[0023] This workbook is illustrated in FIG. 2K and provides a mechanism for the user to either empty the AT Toolset database to start a new subsystem analysis or to transfer data from an earlier version of AT Toolset into this version.
Toolset Setup Workbook
[0024] This workbook is illustrated in FIG. 2L and extracts the Toolset files. It also places a shortcut to this instance of AT Toolset on the Desktop and in the Windows-Start-Programs menu.
Implementation Flow Workbook
[0025] This workbook is illustrated in FIG. 21 and displays the flow diagram describing the functionality and sequence of the various AT Toolset components.
[0026] With reference to FIG. 1, a first step in identifying a tamper scenario for a project, apparatus, method, etc. involves designation of the project, apparatus, method etc. as shown in block 2 which may be identified, for instance as software or hardware. Block 2 may simply document the purpose of the project (including methods or apparatti) to be implemented along with a general breakdown of the thing to be accomplished and/or its work breakdown structure. Block 2 may be, for instance, a document in a spreadsheet.
[0027] Block 4 illustrates critical program information as determined by some other source which, along with critical program criteria from block 5 and information from block 2, rolls up into workbook 6 containing a critical program information tool for determining further critical program information (CPI, information necessary for carrying out the goals of a project).
[0028] Block 7 represents a description of overall threats to project, apparatus or method while blocks 9 and 11 represent descriptions of threats to a project, apparatus or method as furnished for instance by a source, such as a government report. This threat information rolls up into threat vulnerability modules which summarize particular threats and determine vulnerability to a specific threat respectively.
[0029] For the process flow shown in FIG. 1, CPI identification 16 is determined from system description 14 using an analysis method described in block 18. The analysis method is determined by a given process for anti-tamper assessment and implementation 17. Decision tree 20 results in identified CPIs undergoing an impact study based on an asset description and loss impact as determined by asset identification and valuation module 24. System description 14 also takes into account threat description 15.
[0030] Threats described in representative blocks 7, 9 and 11 are analyzed in threat and vulnerability module 26. Threats are summarized in block 28 in terms of critical information.
[0031] Risk evaluation is determined within module 30 using a vulnerability summary 32, attack scenarios 34, exploitation time summary 36, resulting in time factored risk summary 40. Threats from modules 9 and 11 roll up into threat and vulnerability module 42 which provides a vulnerability assessment of the overall project (that is system, method or apparatus) to a threat. Each summary within module 30 is determined by a corresponding module. For instance, attack scenarios 34 are determined by attack module 44; exploitation time summary 36 is determined by asset identification and valuation module 46; and time factored risk summary 40 is determined by risk module 50. Attack module 44 generates attack trees, branched scenarios identified as posing a particular risk to a project. Asset identification and valuation module 46 evaluates the seriousness of a particular threat as it may occur within a given period of time. Risk module 50 makes a time factored risk calculation, Decision tree 52 determines whether the risk involving a particular threat to a project is within an acceptable predetermined risk range. Should the risk be determined to be unacceptable, module 54 user selects potential anti-tamper countermeasures from countermeasures module 56 wherein available countermeasures are defined. Potential anti tamper countermeasures are evaluated within tamper scenarios module 58 which defines tamper scenarios against a project in conjunction with using tamper trees generated by attack module 60. Tamper tree may define potential risks to one or more aspects of a project as it progresses over time, through various phases, etc. Tamper scenarios from module 58 are fed back to risk evaluation module 30 for risk evaluation of a potential threat with one or more countermeasures in place from countermeasures module 56 for a potential tamper scenario defined by module 58. The tamper scenario with the one or more anti-tamper countermeasures in place is fed hack to decision tree 52. Feedback through risk evaluation module 3) is repeated until decision tree 52 deems a particular risk (with or without a particular anti-tamper countermeasure in place) is acceptable.
[0032] Once the risk is deemed acceptable, decision tree 62 determines whether the acceptable risk occurs as a consequence of an anti-tamper countermeasure. Should no anti tamper countermeasure play a part in making the risk acceptable, the anti-tamper processing is adjudged complete at module 64.
[0033] In the instance that the risk is made acceptable as a consequence of one or more anti-tamper countermeasures, solution set module 66 provides anti-tamper concepts from anti-tamper concepts selection module 68. A particular implementation of the anti-tamper concept against a particular threat is provided by anti-tamper implementation module 70 in conjunction with receiving implementation parameters from parameter module 72, Module 74 provides validation and verification of the anti-tamper countermeasure or countermeasures against one or more threats as defined by tamper scenarios module 5l. Module 76 contributes anti-tamper requirement through, for instance, a worksheet to module 74 in conjunction with validation and verification of an anti tamper countermeasure occurring at module 74.
[0034] The provision of one or more anti-tamper countermeasures against a particular threat is adjudged complete by module 64 in connection with documenting the anti-tamper countermeasure against the tamper scenario and level of risk as provided by module N which supplies related supporting information (e.g., glossary definitions used during the processes) and miscellaneous worksheets used in developing determining the anti-tamper countermeasure.
[0035] The workbooks described herein may also be implemented using forms to allow a visual presentation of information to be entered and calculated. In one aspect, a form, such as that illustrated in FIG. 3, may be used to enter information. A worksheet representation of the form may be printed in a PDF format.
[0036] FIG. 4 illustrates an Attack/Tamper tree diagram. Level 0 shows the Asset by number followed direct attacks by number. As shown in FIG. 4, attacks are ordered by number for each asset. At the level 1 attack category, attack 1, attack 4, and attack 5 exists for Asset 1. Level 2 in the At tree diagram lists the countermeasures (CM) by number available to defeat a particular attack/threat. Consequently, CM 2 can defeat attack while CM 5 can defeat attack 5. Attack level following each countermeasure to be employed are outlined in the A tack/Tamper tree diagram, only a portion of which is shown for purposes of illustration in FIG. 4.
[0037] In one aspect, tamper tree diagram generation may occur automatically pursuant to the following:
[0038] Utilization of data records collected in an effort to determine how a particular threat or particular threats may exploit a weakness in a project. In conjunction with this type of exploitation analysis, hierarchical indices may be assigned to individual data elements in each record in order to access the seriousness of a threat.
[0039] Hierarchical indices for each data element in a record may be combined into a single, unique, sortable composite record index in assessing a threat.
[0040] In connection with sorting composite record indices corresponding to, for instance, an attack level, individual hierarchical indices are extracted.
[0041] The hierarchical attack tree structure may be determined from the extracted hierarchical indices.
[0042] Hierarchical indices may be replaced with actual associated data elements and the tamper tree diagram may be displayed as shown in FIG. 4.
[0043] The foregoing may be used to conduct an anti-tamper exploitation analysis pursuant to determining and/or avoiding risks/threats to a project in terms of regarding each risk as a possible project threat or attack, This analysis may proceed according to the following steps:
[0044] 1) Gather pertinent threat, impact vulnerability and attack data records.
[0045] 2) Apply a risk algorithm to data records to assess time-factored risk.
[0046] 3) Based on time factored risk levels, establish possible countermeasure approaches.
[0047] 4) Reassess time factored risk resulting from countermeasure approaches.
[0048] 5) Select the most appropriate countermeasures.
[0049] 6) Select the most appropriate technical implementation concepts for each countermeasure.
[0050] FIG. 5 illustrates a threat/Attack Summary Worksheet for implementing the anti-tamper process toolkit. As shown, threats are designated along with threat names, attack listings, and designation of worst cast scenario.
[0051] Although the invention herein has been described with reference to particular embodiments, it is to be understood that these embodiments are merely illustrative of the principles and applications of the present invention. It is therefore to be understood that numerous modifications may be made to the illustrative embodiments and that other arrangements may be devised without departing from the spirit and scope of the present invention as defined by the appended claims.
User Contributions:
Comment about this patent or add new information about this topic:
| People who visited this patent also read: | |
| Patent application number | Title |
|---|---|
| 20210312089 | DATA AUTHORIZATION INFORMATION ACQUISITION METHODS, APPARATUSES, AND DEVICES |
| 20210312088 | METHOD FOR SHARING AND VERIFYING BLOCKS AND ELECTRONIC DOCUMENTS BETWEEN NODES IN BLOCKCHAIN |
| 20210312087 | METHOD FOR MONITORING THE INTEGRITY OF A PHYSICAL OBJECT |
| 20210312086 | APPARATUS AND METHOD FOR RECOMMENDING USER PRIVACY CONTROL |
| 20210312085 | Electronic Devices, Methods, and Systems for Temporarily Precluding Sharing of Media Content to Protect User Privacy |