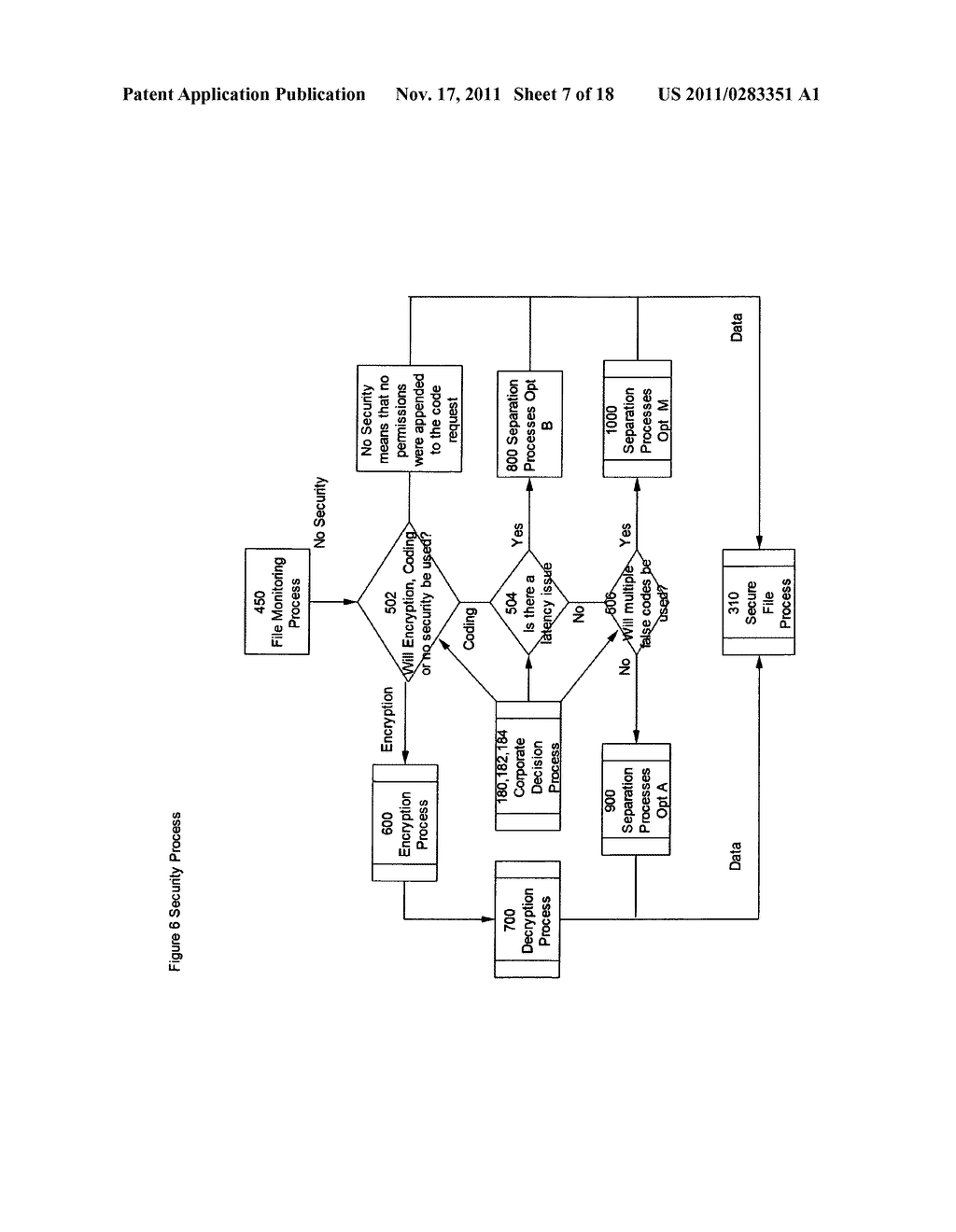
How to stop external and most internal network "Hacking"attacks by utilizing a dual appliance/server arrangement that allows for the use of peering servers and/or client software running on said peering servers or on proxy servers, web servers, or other legacy equipment - diagram, schematic, and image 08
Back to How to stop external and most internal network Hacking attacks by utilizing a dual appliance/server arrangement that allows for the use of peering servers and/or client software running on said peering servers or on proxy servers, web servers, or other legacy equipment , All Patents .
