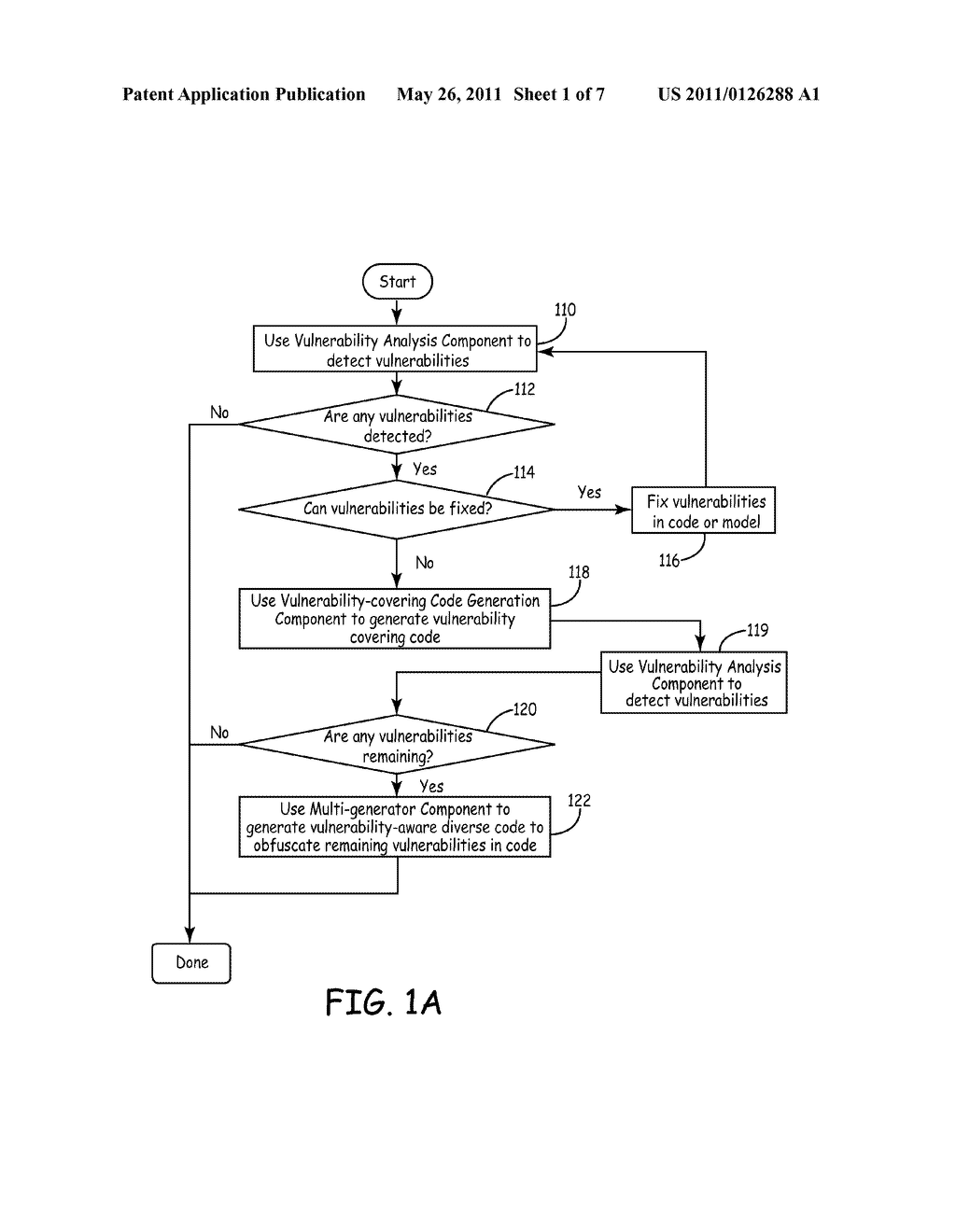
METHOD FOR SOFTWARE VULNERABILITY FLOW ANALYSIS, GENERATION OF VULNERABILITY-COVERING CODE, AND MULTI-GENERATION OF FUNCTIONALLY-EQUIVALENT CODE - diagram, schematic, and image 02
Back to METHOD FOR SOFTWARE VULNERABILITY FLOW ANALYSIS, GENERATION OF VULNERABILITY-COVERING CODE, AND MULTI-GENERATION OF FUNCTIONALLY-EQUIVALENT CODE , All Patents .
