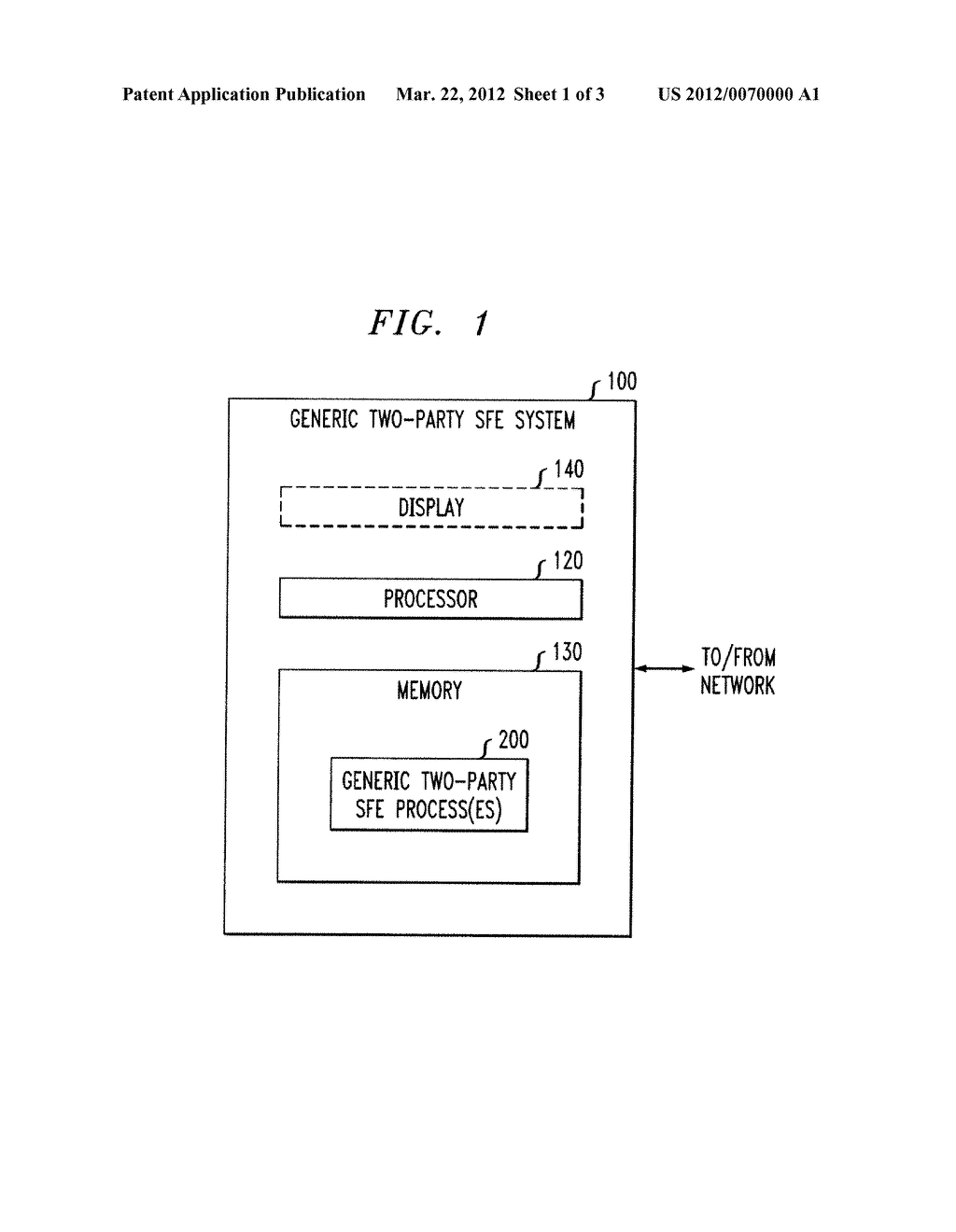
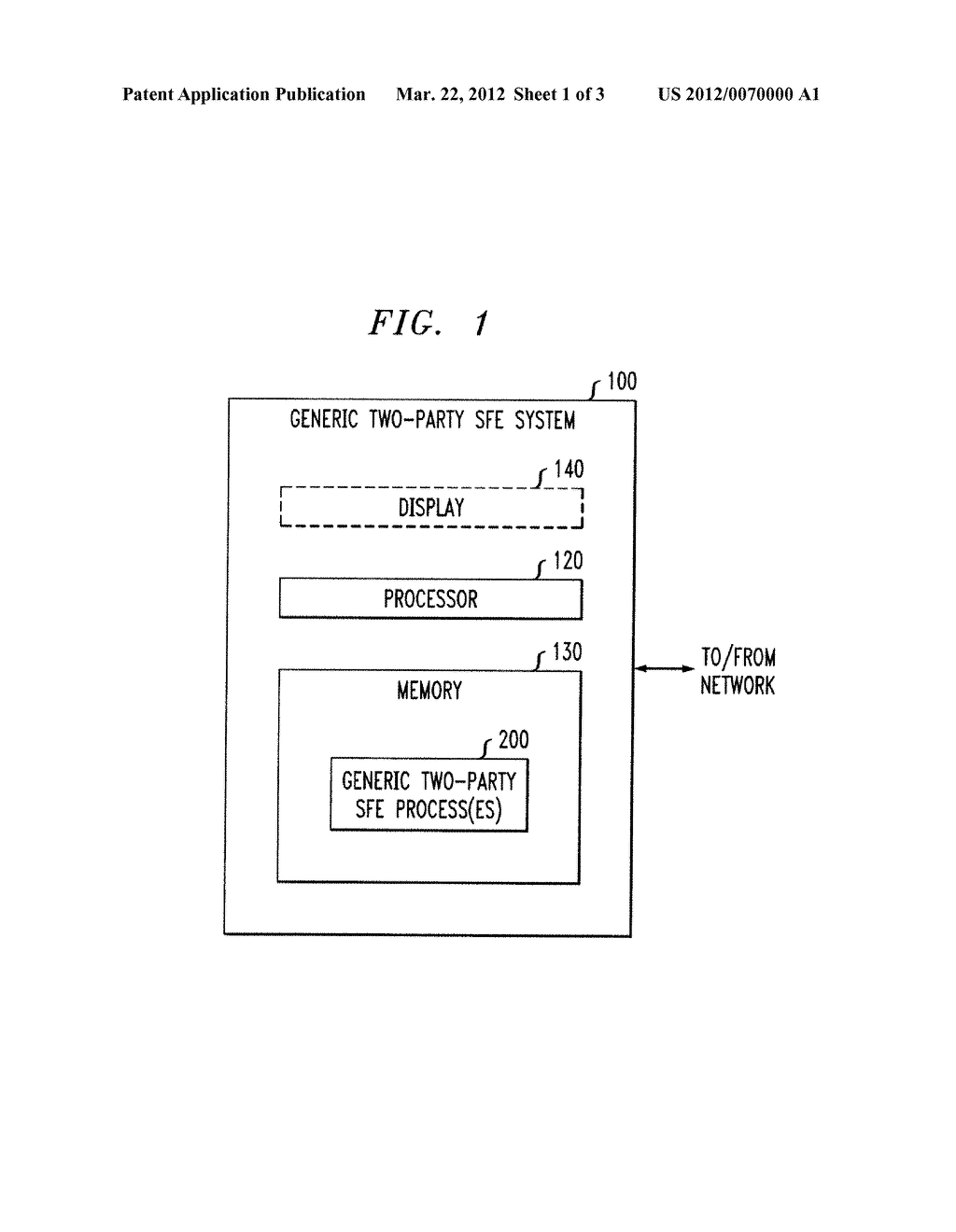
Securing Two-Party Computation Against Malicious Adversaries - diagram, schematic, and image 02
Back to Securing Two-Party Computation Against Malicious Adversaries , All Patents .
Back to Securing Two-Party Computation Against Malicious Adversaries , All Patents .